Table of contents
Recently we interviewed someone who had their smart home cameras hacked. The attackers in this case managed to bypass the standard password credentials on the IoT device services. They used this to spy and harass this person and their family. A hacked camera was all it was. Luckily, nothing else happened beyond that. The perpetrators could only harass the victim with verbal abuse. But the emotional damage took its toll.
Similar to a Prank Call
This particular case took place in California. Authorities were contacted. They managed to back trace the source. Turned out that the attack originated from the Europe. Apparently, a small group of online gamers decided that they had nothing else better to do. Except harass, insult and intimidate through petty spying. Unfortunately, problems related to foreign legal jurisdictions are still delaying the victims from achieving justice.

No Vendor Remittance
The manufacturer of the smart camera was also rather quick to throw their own customer under the bus. By blaming the end-user, they refused to accept any form of responsibility. The reason why they do this is because anything that leads to questioning their devices is perceived as a risk to profit. They have every incentive to protect revenue streams. So the victim was left feeling powerless. While the perpetrators made them feel like their house was haunted. Sometimes even only targeting one member of the family at a time, to instill fear. Its difficult to imagine that this could happen, but there are many horror stories coming out from people who have had similar issues.
Media Spinning
Media reports also gave little credit to said individuals who tried telling their story. Every major cable broadcast network framed it from an angle that blamed or even mocked the smart camera consumers. The victim was left in a state of further grievance because this added insult to injury. It became hard for them to stand up for themselves, and understandably so. No one should have to go through that. Everyone deserves to feel safe in their home. But the problem is that no one was capable of delivering a firm resolution. Its worth mentioning that if IoT device manufacturers worked more closely with Simius, they could reduce their risk and make easier improvements to assist consumers with smart home security. We want to make this as seamless as possible. Mistakes can be made, but the course of correction is most important is the course to correction.

Who You Gonna Call?
Imagine feeling like you’re living inside a haunted house. There are voices shouting profanities at you, making threats. It would be terrorizing for anyone. But remember, it says nothing about you as a person. If anything, the perpetrators are below any level of civility. So the only thing that matters is the path forward, in preventing these things from happening. Trapping them. As mentioned in a previous blog article, the only way to defeat a hacker is to think like one. Simius is your first step in achieving this. We help identify the problems before they happen but even if they are active threats.
Call Upon Yourself First
If your smart home camera is hacked and someone is harassing you from the other end, first thing to do is disconnect the device from the power source. Your other devices likely might not have been compromised, but be sure to change passwords and update all firmware regardless. Consider making a separate wi-fi network for those untrustworthy IoT devices. Its what the pros do. Some of these IoT devices simply cannot be trusted due to the minimal resources applied in making them work.
Make No Assumptions
Maintaining a sense of vigilance in cyber space means that you recognize the end-points of your home network, and that makes it easier to secure your devices. There are only two ways into your smart home devices, but both are vastly different in circumstance. The first is through the wired internet connection, where anyone can see the list of public IP addresses that routers use to connect online. That means anyone from around the world can potentially attack your router. The second is wireless, and where a hacker is within physical range of your wi-fi, Bluetooth, or other wireless devices (this is known as wardriving).

Gain Cyber Intel
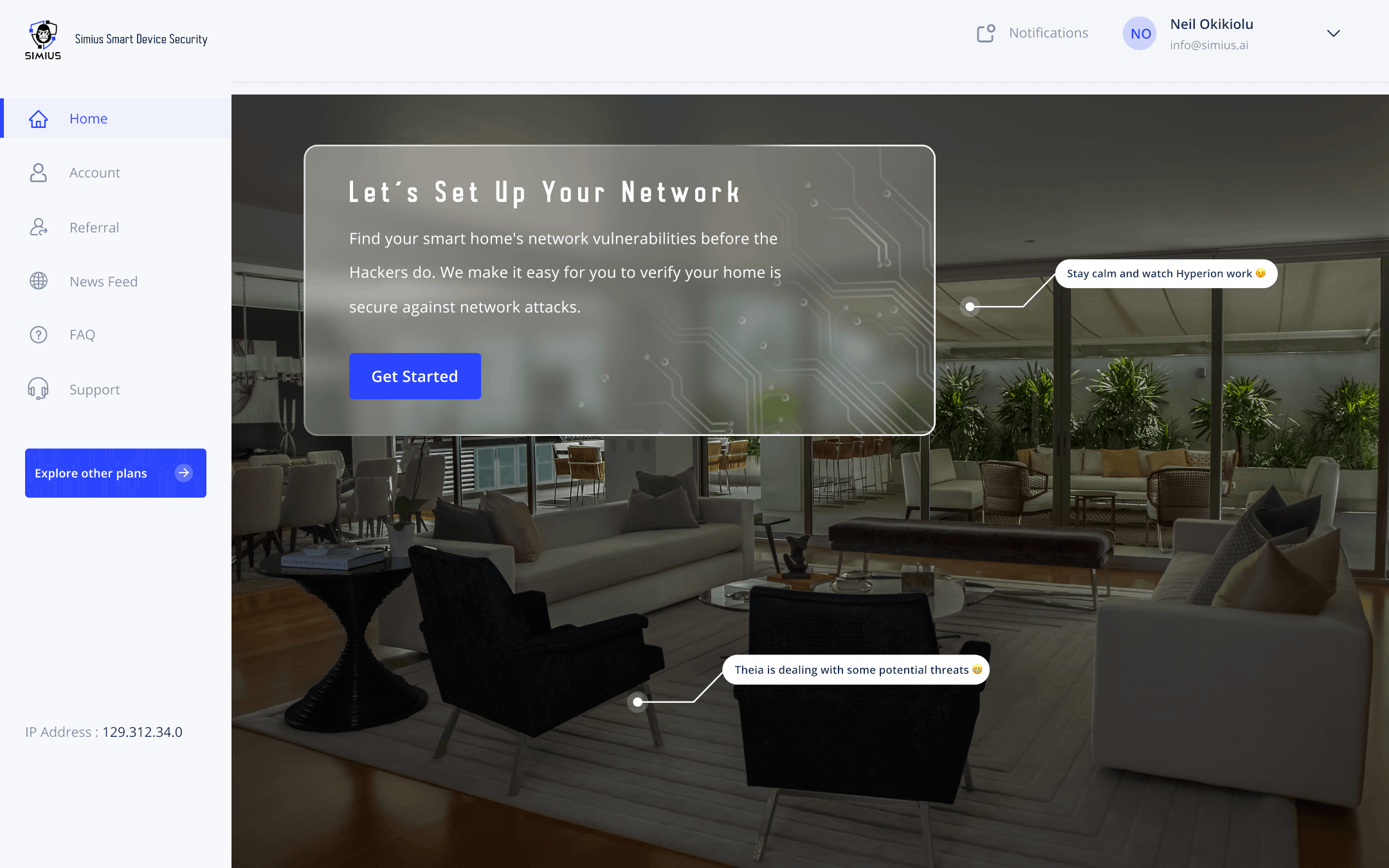
When knowing is half the battle, you are set. Being aware of the problem allows you to further take control over any disastrous situation. Actionable information is often invaluable. A course of action can be identified to correct the issue. A hacked camera can do a lot more damage than it is worth. The intent with Simius is to empower our customers with this valuable information by testing smart home network security using the same methods as the hackers. Solutions and recommendations are also provided for a clear reckoning of resolving the problem.
Before you can think like a hacker, assume you have already been breached or compromised. Do not assume anything else until the questions are validated. Ask yourself a few things. Is my firmware and software up to date? Have I changed the default passwords on my devices? Did I click on any suspicious links on email or text message? Do I have separate wi-fi networks with different passwords to isolate untrusted IoT devices? Though it might seem counterintuitive, the answers here will help fortify your position on the internet. The only way to know is through testing the security of your network. Simius can do that and notifies you on a schedule by default. So you can keep it on a schedule with any other form of smart home automation.

That’s The Way It Is
Sometimes manual intervention is necessary. Updating your router might be as simple as unplugging it for a few minutes and then plugging it back in. But other routers could potentially need you to log in on the device and install the updates. The same might be true for other connected devices. A hacked camera is the best example. Changing your passwords consistently and keeping them complex will also help. So having knowledge about a vulnerability or threat is what gives you the ability to resolve a potential problem on your home network.
Ultimately, our goal is empowerment of smart home owners and IoT consumers alike. There is a wide range of cyber criminals seeking to exploit your devices, each with their own motive. Regardless, the first step towards adopting vigilance in cyber space is to acknowledge the risks while identifying and fixing them as well. It does not need to be any more complicated than that. No sense in overthinking the problem. Don’t let a hacked a hacked camera spoil your appetite for convenience with IoT devices. Whether someone is trying to commit identity theft, or they are pranking, you can leverage our resources from Simius to shield yourself from such risks.
Learn to Adapt and Overcome
As with any technology, it is a double-edged sword. Whether it be smart devices themselves providing convenience but coming with security flaws, or hacking tools being used by either criminals or ethical hackers. The best choice is to get the best of both worlds. Convenience and security can be easily done with proper maintenance. Attention to the important details, while using the same tools the hackers use to test your cyber defenses is your best bet.

Believing in your own system is crucial. Technology is not made simple enough for everyone to understand. Luckily there are cybersecurity professionals who understand this gap and are willing to act on behalf of others who don’t know any better. Simius is standing tall on that front line. We’ll help you eat these cyber criminals for lunch, because we eat them for breakfast. Especially when getting hacked, it feels like you made a huge mistake. Simius will help empower you to correct those mistakes, if any. You don’t know what you don’t know, and sometimes it takes a rude awakening. Try not to take it personally, but rather deal with the situation as any professional would. Power through the difficulties and remain vigilant. Stay sharper in smart home cybersecurity, with Simius.
Summary
In this article, we discussed the situation of having smart cameras breached, from the perspective of an ethical hacker, and how you can take action to prevent such things from happening.