It was the summer of 2017. My company had been crippled by a multi-pronged ransomware cyber-attack. We were totally overwhelmed. All of the files, operating systems, and applications were rendered completely useless. Production was brought to a complete halt. Engineering couldn’t launch their applications nor could Accounting. We were also in the middle of moving offices. Its like the criminals couldn’t have hit us at a worse time.
As a result, production was halted and the company losing about $3,000 per minute. The cost of downtime can be immense for a lot of companies.1 All we had to do was pay a $300 ransom in Bitcoin, but since when did trusting cyber-criminals ever become a good idea? Remember, if it sounds too good to be true, then it probably is. So you better have a disaster recovery strategy and have it better than the worst case scenario.
Shown below is similar to the screen we were given upon boot of each infected PC. You might ask again, how did they get infected? Simple, computers were left online during early morning prior to business hours, but someone came in early, and clicked a phishing email by accident. At least that is what is suspected, since more than 90% of successful cyber-attacks begin with a phishing email.2

Petya was previously documented.3 But it was only ply-and-part of the payload. We saw elements of WannaCry being embedded with Petya.
A lot has happened since then. We mostly recovered from this disaster, and within a few days but it was quite the crisis. It took several months to fully repair all of our systems. And at least we were able to get things back to business as usual. But we’ve had to train and protect our staff in order for them to remain aware, because they are the first line of defense. All users ultimately become first-class stakeholders in that regard, since strategies need to be adopted in order to fulfill our end of the bargain. The open wild is evolving and rapidly shifting by the day.
It is easy to be unprepared, despite having the latest and greatest software and hardware technology. Sometimes it won’t matter if you have a physical firewall, and apart from decent anti-virus definitions being up-to-date, there are limited options on the market. That wasn’t the problem. All it takes is a simple phishing email was likely clicked by an end-user, which then allowed a hydra worm to penetrate the network firewall. The worm likely used some sort of raindbow-table method to bypass administrative permissions on the network where it then dropped its payload on all available machines. A rainbow table is a precomputed table for caching the output of cryptographic hash functions, usually for cracking password hashes.4
The consequences of user error can be catastrophic, and it is important to do a basic level of training in order to recognize patterns indicative of security risk.
Our Threat Repository is meant to offer a knowledge-base for our users to leverage against cyber security risks with an added advantage. Knowing is half the battle, thus the goal is to help educate our users so that they can be empowered.
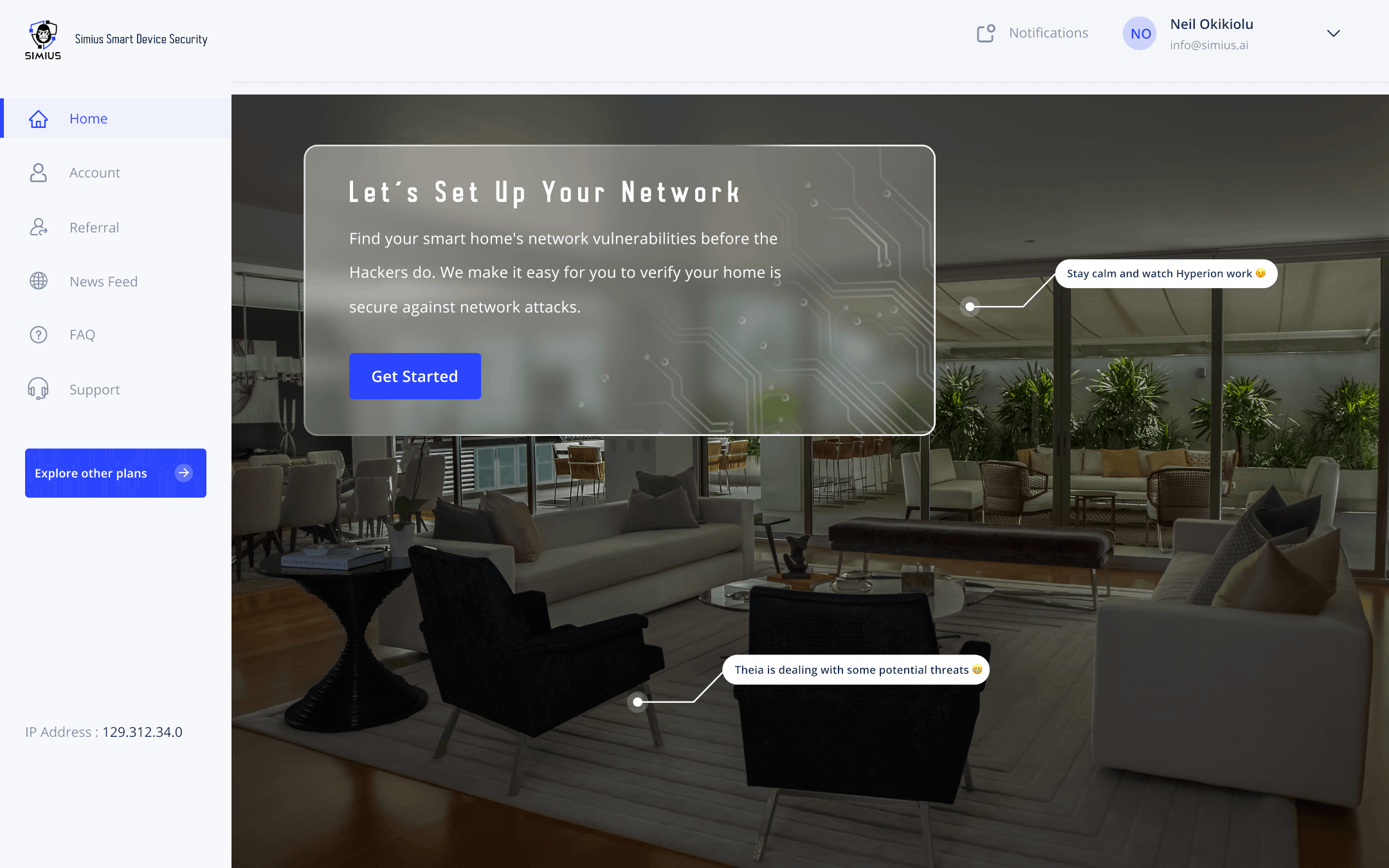
Scare tactics work, but the only way to resolve a situation beyond your control is to never give in, and always have a backup plan. Be prepared by testing that plan on a consistent basis. That is where Simius can help. Our methods are setup to one-click this exact functionality at your fingertips using enterprise-grade cyber security software technology, which can take teams of professionals to operate. One must incorporate tact and care into the strategy, with thorough analysis, planning, time, as well as materials to ensure operational success during disaster.
With Simius, our goal is to imitate the cyber criminal as best as possible. We do this by simulating the cyber attack itself, and gather this data to build a profile on your IoT systems to build the necessary shielding. While our projects to secure the IoT platform, we keep a library of relevant threats open and available on our website while automating these various cyber-attack vectors through our scans – So that you don’t have to worry about it. This helps to eliminate vulnerabilities and prevent performance drain associated with traditional antivirus software.
It also allows us to keep a remote profile secured externally to your systems, which is a form of decoupling. This reduces security risks while improving performance. That profile is logged within our cloud database and allows us to detect vulnerabilities which can then be patched on those devices.
Moral of the story is, resist the urge to panic and make sure that you’ve trained yourself to understand the nature of each system you use. At the same time, let the professionals handle the worst-case scenarios. The internet was built to be shared. Security was never really considered, and in that paradigm lies a larger problem.
A can of worms was opened and it just so happened to be yet another Pandora’s Box. So this is nothing new, since all technology can be viewed as a double-edged sword. Many flaws come with this flimsy network architecture however, which makes users susceptible to almost every conceivable form of cyber threat. But fear is the mind-killer, and cyber criminals feed most upon fear. We must stay ahead of the game. Beat them at all costs, to protect your privacy, safety, and security.
With Simius, we add to your existing tool set with automated smart device security testing.
In my professional experience, I can say that planning is absolutely critical. The same is true for testing. On top of that, you need to train longer and harder than your enemies if you wish to survive. At Simius, we want to automate that training so that it is simplified for you, while making things more complicated for cyber-criminals. Reduce risk through a multi-pronged approach – that is all I can say, aside from the best is yet to come.
- The Cost of Downtime – Gartner – https://blogs.gartner.com/andrew-lerner/2014/07/16/the-cost-of-downtime/ ↩︎
- More than 90% of successful cyber attacks worldwide begin with a phishing email – IT Governance USA Blog – https://www.itgovernanceusa.com/blog/more-than-90-of-successful-cyber-attacks-worldwide-begin-with-a-phishing-email ↩︎
- Petya malware – Wikipedia – https://en.wikipedia.org/wiki/Petya_(malware) ↩︎
- Rainbow Table – Wikipedia – https://en.wikipedia.org/wiki/Rainbow_table ↩︎